77% of Australian CISOs are investing in AI governance as machine-speed threats force a resilience rethink
At ADAPT’s 12th Security Edge in Melbourne, more than 150 security leaders tackled the shift from prevention led cyber security to resilience built for machine speed threats.
Securing autonomous systems now depends on how quickly organisations can govern AI, contain compromise, and keep critical operations running under pressure.
Cyber security has moved beyond prevention as the main measure of enterprise risk.
Attackers are accelerating, AI systems are creating autonomous pathways through organisations, and operational environments are becoming harder to isolate.
CISOs now need to prove the business can detect, contain, recover, and keep operating when compromise occurs.
At ADAPT’s 12th Security Edge, held at Park Hyatt Melbourne, more than 150 security leaders examined how organisations must adapt as compromise becomes faster, AI systems become more autonomous, and critical environments become harder to defend.

The cohort represented organisations responsible for protecting over one quarter of Australia’s GDP and 8% of the national workforce.
ADAPT Founder and CEO Jim Berry sharpened the urgency in his opening address, warning that adversary breakout times have compressed to 27 minutes, a 65% acceleration from the 48-minute figure cited the previous year.
He framed compromise as an operational reality rather than a remote scenario, with resilience measured by an organisation’s ability to maintain services, limit impact, and recover at the speed now required.
That pressure is exposing structural weaknesses across many organisations.
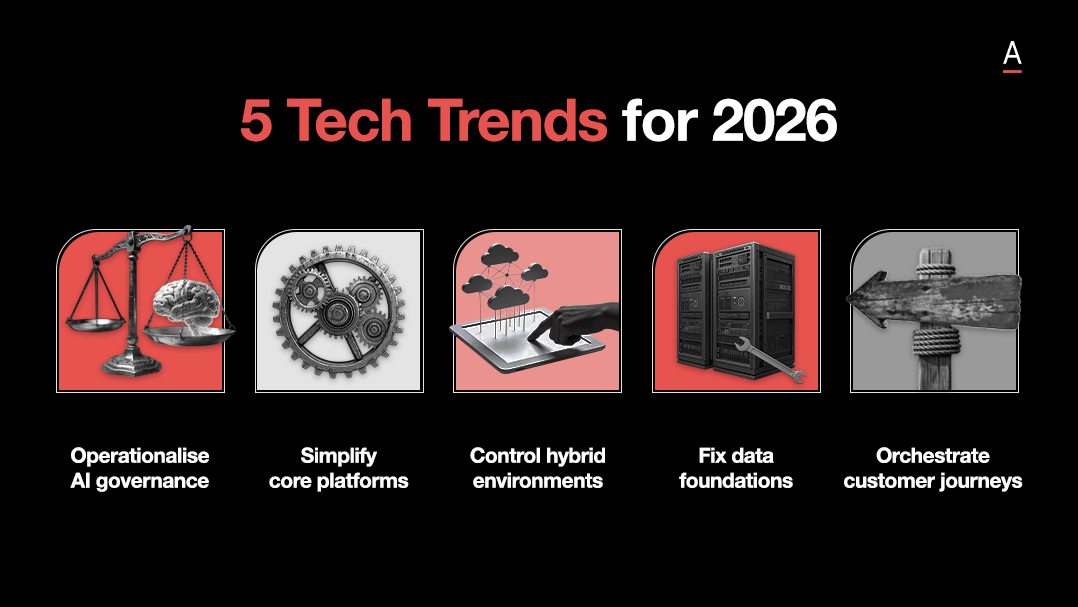
AI adoption is scaling faster than governance, security teams are managing fragmented operating models and legacy environments, and many businesses still lack the resilience discipline required to operate at machine speed.
Across ADAPT research, executive keynotes, practitioner case studies, and CISO panels, one pattern stood out.
Security leaders are being pushed from prevention leadership into resilience leadership, while AI governance, OT oversight, cloud ownership, tool consolidation, and breach response discipline become part of the same operational challenge.
Redesign resilience for machine speed compromise
The strongest shift across Security Edge was the collapse of the traditional prevention first security mindset.
As adversaries accelerate and operational environments become more interconnected, resilience can no longer depend on slow escalation paths, fragmented ownership, or manual response processes.
The operating question becomes whether organisations can absorb disruption, contain impact, and maintain critical services while incidents are still unfolding.
Gabby Fredkin, Head of Analytics & Insights at ADAPT, showed why many organisations are struggling to make that transition.

Based on 1,000+ regional surveys of Heads of IT, Digital, Security and Finance, he revealed organisations continue to face structural barriers including competing priorities, funding constraints, staffing gaps, and legacy environments.
AI is now exposing weaknesses in governance, accountability, and workflow maturity much faster than organisations can adapt.
The pressure is accelerating quickly.
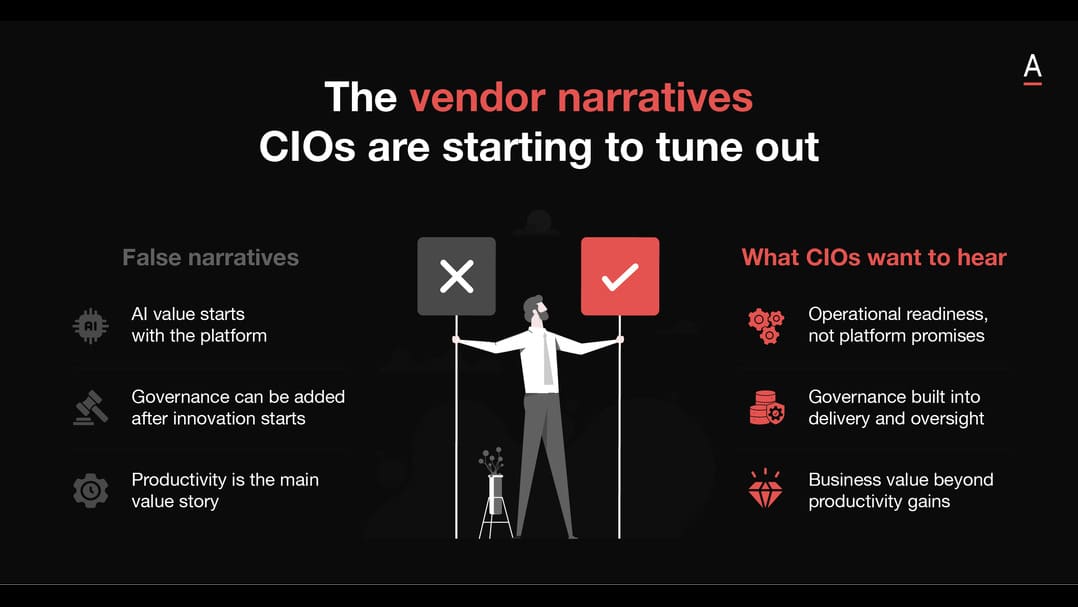
ADAPT research revealed that 77% of CISOs are investing in AI governance in 2026 because AI adoption is scaling faster than organisational control models.

At the same time, many organisations are still trying to modernise resilience using operating structures designed for slower, more isolated threats.
That tension becomes even sharper under constrained budgets.
In conversation with David Gee, ADAPT Advisor and influential CISO, Adam Cartwright, CISO at Australia Post, argued that resilience improves when security leaders focus investment on the controls most likely to reduce real world attack paths rather than attempting broad uplift across every control domain.

Drawing on experience across banking, FMCG, and Australia Post, Cartwright pointed to credential compromise as one of the most consequential operational risks because attackers continue to target the simplest pathways into enterprise environments.
Collectively, the discussions pointed toward a broader operating model shift.
Resilience is increasingly becoming a speed and prioritisation problem, where security leaders must continuously decide which risks materially affect operational continuity and which controls create measurable reduction in exposure.
Govern AI before autonomous risk scales
AI governance emerged as one of the defining operational challenges across the event because organisations are now scaling experimentation faster than they can scale oversight.
Many security leaders are facing environments where AI adoption is already spreading across workflows, decision making, and operational tooling while governance structures remain fragmented or immature.
Gabby highlighted that many organisations still lack clear visibility into how AI systems are being used, what data they access, and how outputs are being validated.
The challenge is not simply technical governance.
It is organisational behaviour.
As AI tools become easier to deploy, security teams are under pressure to create controls that guide adoption without slowing the business to the point where teams work around them.
During the Security Edge panel discussion, Mark Alexander, CISO at ASD, argued that governance structures creating excessive friction ultimately encourage bypass behaviour and shadow adoption across the organisation.
Instead, he pushed for practical governance models that embed security into decision making early while still allowing experimentation to continue at speed.

That same theme surfaced differently through Sam Fariborz, CISO at David Jones, who discussed establishing simplified AI usage principles before experimentation accelerated further across the business.

Rather than treating governance as a downstream compliance exercise, the focus was on building repeatable expectations around access, accountability, and responsible usage before inconsistency became harder to control.
Darren Kane, Chief Security Officer at NBN, extended the discussion beyond governance into operational responsibility.
For security leaders, the challenge is now dual layered: organisations must govern AI adoption safely while also using AI internally to strengthen security operations and resilience capability.

That creates a more difficult operating environment for CISOs because AI is simultaneously becoming a productivity driver, a governance challenge, and a new attack surface.
William MacMillan, former CISO of the CIA and former SVP of Information Security at Salesforce, argued that organisations remain too early in the AI maturity curve to hand critical operational decisions entirely to autonomous systems.

His perspective centred on maintaining human accountability inside security operations, particularly as AI models still struggle with contextual judgement and explainability.
These sessions reinforced that AI governance is rapidly evolving into an enterprise operating discipline rather than a standalone cyber policy function.
Identity, evidentiary controls, auditability, operational authority, and human oversight are all becoming interconnected parts of the same governance challenge.
Modernise OT and cloud security as business continuity risk
Security Edge also reinforced how tightly cyber resilience is now tied to operational continuity.
As OT systems, cloud infrastructure, customer operations, and AI enabled workflows become more interconnected, security incidents increasingly carry direct operational and commercial consequences.
ADAPT research showed that 44% of Australian organisations now operate OT environments requiring significant or business critical cyber oversight.

That dependency is forcing organisations to modernise infrastructure while still maintaining uptime across highly sensitive operational environments.
Darren Kane made the scale of that challenge tangible through the NBN environment, where operational disruption carries national level implications due to the volume of Australia’s network traffic traversing the infrastructure daily.
At the same time, many organisations are discovering that large scale replacement programs create their own operational risks.
Gabby Fredkin noted that resilience strategies are increasingly shifting toward simplification, isolation, visibility, and continuity planning rather than complete infrastructure replacement.
That same balancing act is reshaping cloud security operating models.
Stefan Shrekat, CISO at Reece Australia, described how fragmented security ownership and inconsistent workflows had made cloud risk management difficult to scale effectively across delivery teams.
The organisation responded by embedding greater visibility and accountability directly into engineering environments so developers could work with contextualised security insights earlier in the workflow.

Daniel Kreitals, Senior Solutions Engineer at Wiz, reinforced that modern cloud security models increasingly depend on shared visibility between infrastructure, engineering, and security teams rather than isolated escalation processes.
The broader shift emerging across both OT and cloud environments is that resilience can no longer sit separately from operational design.
Security leaders are now being asked to help architect continuity directly into infrastructure, delivery pipelines, and operational decision making.
Consolidate tools without concentrating failure
Tool fragmentation emerged as another major operational weakness throughout the event.
Security teams are managing growing alert volumes, disconnected workflows, duplicated tooling, and increasingly complex operating environments at the same time as AI is accelerating both attack speed and response expectations.
ADAPT research revealed that 75% of Australian organisations are exploring or actively pursuing security tool consolidation as teams attempt to reduce operational complexity and governance overhead.

The appeal is understandable.
Consolidation promises simplified workflows, lower management burden, and faster visibility across environments.
But the discussions throughout Security Edge repeatedly returned to the trade-off emerging underneath that shift: reducing fragmentation can also increase dependency on a smaller number of platforms and providers.
William MacMillan argued that AI is already delivering measurable gains in investigation speed and operational efficiency inside security operations environments.
However, he warned against assuming faster automation automatically translates into better operational judgement.
AI systems may compress analysis time, but organisations still need explainability, evidentiary controls, and human oversight around how decisions are being made and executed.
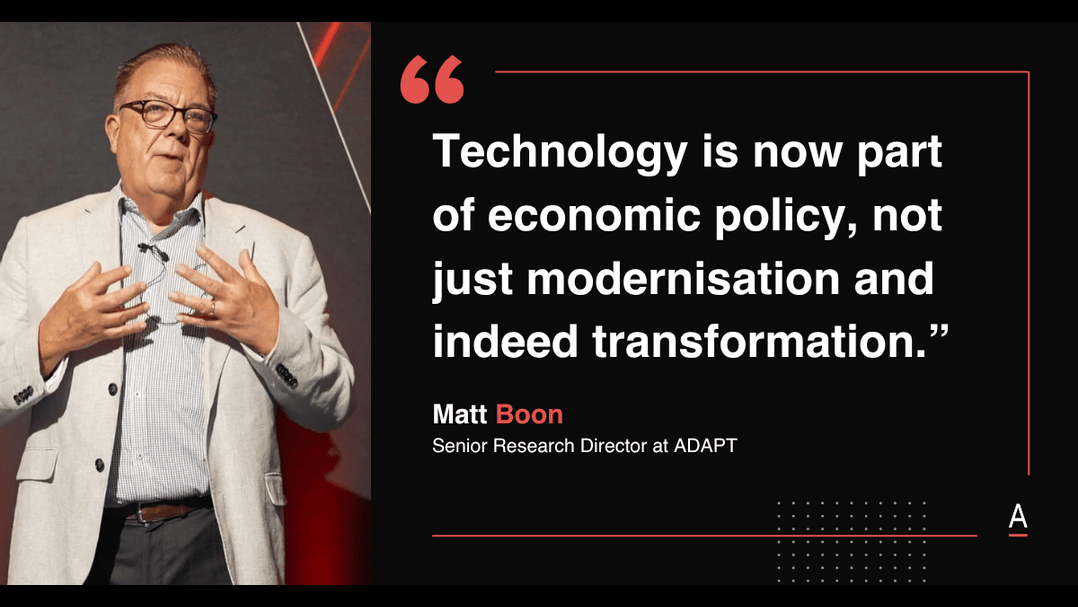
Matt Boon, Senior Research Director at ADAPT, contextualised that pressure through the operational realities security leaders are facing daily, including constrained staffing, operational fatigue, and rapidly expanding attack surfaces.

The underlying challenge is becoming increasingly clear.
Organisations want simpler environments and faster decision making, but they also need to avoid creating concentrated operational risk through excessive dependency on opaque platforms or poorly governed autonomous systems.
Lead breach response with proof, trust, and human accountability
Alex Loizou, Cyber Security Leader at Intrinsic Security, looked back on leading Medibank’s cyber response during the 2022 breach brought the conversation back to the human and organisational pressures created when incidents move beyond playbook assumptions.

One of the clearest themes from the session was that resilience becomes a leadership discipline long before it becomes a technical recovery exercise.
Once incidents escalate publicly, organisations must simultaneously manage operational response, executive communication, regulatory engagement, customer trust, and team sustainability under sustained pressure.
Alex described how the organisation implemented rotating executive shifts, separated business as usual operations from incident leadership responsibilities, and introduced multiple independent incident response partners simultaneously to validate investigative findings and improve confidence in decision making.
That emphasis on validation and proof carried through the broader discussion around trust deficit.
Following a public breach, organisations are required to rebuild confidence simultaneously across customers, regulators, boards, employees, and external stakeholders.
Remediation therefore becomes more than fixing technical gaps. Security leaders must also demonstrate measurable progress, operational accountability, and visible assurance throughout recovery programs.
Sam Fariborz connected that idea back to organisational culture and partnership.
At David Jones, she discussed working closely with store risk, physical security, and health and safety teams because those functions already operate with mature risk behaviours and operational accountability models.
The implication was that resilience improves when cyber security becomes embedded into broader organisational risk disciplines rather than operating as a separate technical function.
Security leaders are now being asked to govern autonomous systems, maintain operational continuity, absorb compromise, modernise infrastructure, and preserve organisational trust simultaneously.
The role itself is expanding from technical protection toward operational resilience leadership.
Recommended actions for security leaders
The priorities that emerged across Security Edge were practical and operationally focused.
Security leaders preparing for increasingly autonomous environments are concentrating on a smaller set of execution disciplines that strengthen resilience, improve governance, and reduce operational friction during incidents.
- Redesign incident response models around operational continuity, not only prevention and containment.
- Establish AI governance frameworks that support adoption at scale while maintaining accountability, visibility, and human oversight.
- Reduce fragmentation across security, data, infrastructure, and operational teams to improve decision speed during incidents.
- Prioritise visibility across OT, cloud, and AI environments before expanding automation further.
- Consolidate tooling carefully to simplify workflows without creating concentrated operational dependencies.
- Build evidentiary controls, auditability, and explainability into AI enabled security operations.
- Create leadership rotation and operational support structures that can sustain teams through prolonged incidents.
- Measure resilience through recovery capability, continuity readiness, and organisational trust, not only prevention metrics.
The next test for security leaders is how much resilience they can build into the organisation before pressure arrives.
As AI agents move deeper into enterprise workflows, OT environments carry greater operational consequence, and cloud delivery teams own more of the attack surface, resilience has to be engineered into how the organisation decides, operates, and recovers.
The leaders who move fastest will be those who can turn governance into speed, proof into trust, and security accountability into a shared operating discipline before the next disruption exposes the gap.