The Australian government tells companies never to pay ransoms to cybercriminals like those that hacked Optus and Medibank, but most companies ignore that and pay up. There are no laws against it.
According to a report by cybersecurity firm Kaspersky, almost 80 per cent of businesses globally that were hit with ransomware, where a hacker makes company systems or data inaccessible until a payment is made, complied with the demands. Almost 90 per cent of businesses previously hit would pay again.
Their reasons include avoiding the reputational hit from disclosing a hack, customers taking their business elsewhere and the cost of fixing up faulty digital infrastructure.
But the Australian government’s position is clear: those reasons are not good enough.
“The formal advice of the Australian Government is don’t pay ransoms,” Home Affairs Minister Clare O’Neil said on Thursday.
These people are hard criminals and they are dishonest. They’ll tell you all sorts of things about what will happen in the aftermath of paying a ransom and by nature these people are liars and we suggest not co-operating with them.”
Asked by a reporter whether it was illegal for firms to pay, O’Neil, who is also the cybersecurity minister, said: “no”.
Until the federal parliament passed, and then upgraded, cyber laws in recent years companies did not even have to report succesful cyber attacks on critical infrastructure to the government. Other firms are still under no such obligation.
Optus has said it did not pay a ransom while Medibank has declined to discuss even the size of the ransom demanded, citing an ongoing federal police investigation.
In each case, the firms were not hit with ransomware in a technical sense, because their data was still available for use but appeared to have been copied and downloaded by criminals.
That is unlike some of the most expensive ransomware demands.
Taiwanese computer manufacturer Acer faced the largest known ransomware demand early last year, after hackers asked for $US50 million, and then increased their demand to $US100 million ($160 million) if the company didn’t pay up within eight days.
Acer made a counter offer of $US10 million, which the group rejected. It is not known whether Acer eventually paid the ransom.
Global meat processor JBS Foods paid $14 million last year to end a ransomware attack that had disabled its plants in America and Australia, threatening meat supplies for supermarkets.
Colonial Pipeline, a company that supplies about half of the gas to the United States’ east coast, paid $7 million in bitcoin to end another ransomware attack in the same year.
Paying the ransom meant it could begin operating its pipeline but that wasn’t how it worked out: Bloomberg later reported that the decrypting tool the hackers provided the operator to restore its computer network was so slow that Colonial ended up using its own backups to restore the system.
Australian reformed hacker Bastien Treptel said that was characteristic of hackers. “Hackers are amazing at breaking things, but they’re not so good at putting things back together,” said Treptel, who hosts the Cyber Hacker podcast.
Treptel added that because information technology systems in Australia are often poorly set up and maintained, when a company faces an attack, they often don’t have the backups to restore their systems. That means paying the ransom is often the only option available to organisations to recover.
It’s a pretty poor excuse to not be able to recover from a ransomware attack,”
he said, noting that best practices in maintaining computer systems have existed for years.
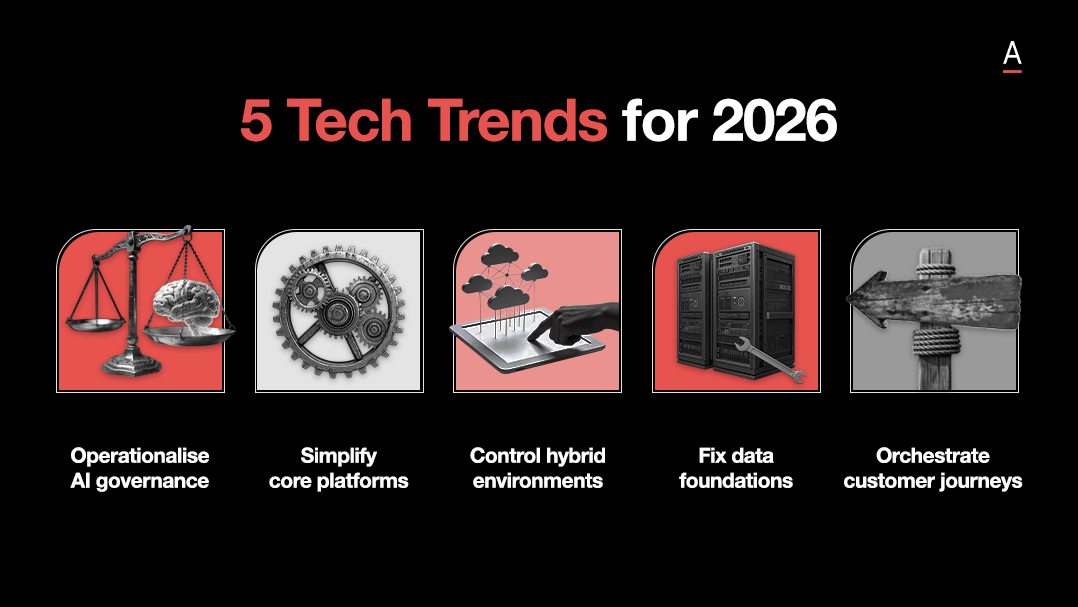
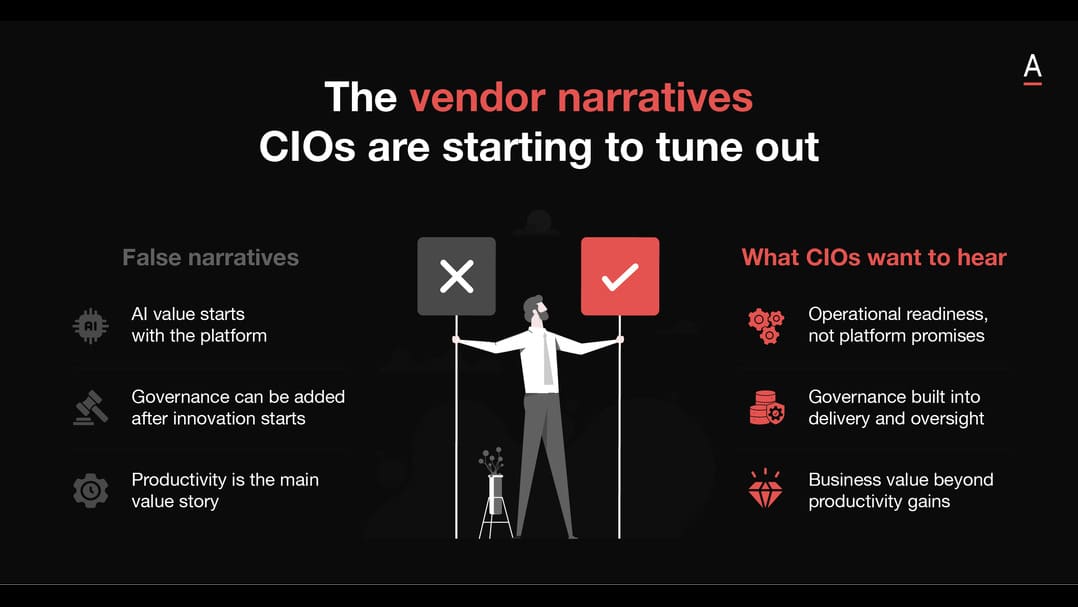
Matt Boon of cyber firm ADAPT said companies like Medibank were in a no-win situation because paying a ransom could encourage more breaches. But there were reasons why it might pay.
They may have no choice but to bow to immense pressure from the public and the government to retrieve the information at any cost. Medibank’s efforts to minimise the potential damage of this breach and communicate to its’ customers the impact on them in a clear, constructive way in the coming hours and days is vital to maintaining their trust”.
There are no explicit rules for companies on the Australian Securities Exchange to disclose whether they’ve paid a ransom. Instead, companies are bound by their obligation to disclose an event if it would have a material impact on the price their shares.
Co-chief executive of cybersecurity firm Internet 2.0 Robert Potter, who has worked with a host of major companies on breaches, said that contrary to many surveys’ conclusions most companies don’t pay ransoms, as cyber criminals often hit multiple targets to guarantee a payout.
Strategically, Potter said, it’s a bad move for a company to pay a ransom especially because it could be unsuccesful.
“There are laws in Australia that could be enforced against a company that pays a ransom, but there isn’t an example yet of someone having one of those laws being enforced as a result of the [payment of] a ransom in Australia,” he said.
Those laws include rules against financing terrorists, sanctioned countries such as North Korea that are known to engage in cyber crime for profit, or other criminal activity. There are defences that could apply in some cases, rendering it a legally complex area.
While cyber criminals face length jail sentences if caught, many are based overseas, making the process of investigating and prosecuting difficult but not impossible.
British police arrested seven people in March over a series of hacks which targeted major firms including Okta and Microsoft, both based in the US. A former Amazon engineer was charged earlier this year with seven counts of computer and wire fraud for carrying out a major hack on Capital One Bank in 2019.
Early this month, Federal Police arrested a 19-year-old in relation to an alleged scam carried out following the Optus hack, though they are not the actual hacker.
”If you make one mistake [as a hacker], like not turning a VPN on or using a MAC address tracker, the international forces are coming down,” Treptel said.