The transition to remote working has placed immense pressure on IT teams and infrastructure from the network layer to the data centre, with tens of thousands of new WFH endpoints, accelerated scale to multiple clouds, VPN challenges and security gaps.
Australia has faced more attack campaigns, continued nation state threats, and the increasing cost and impacts of breaches or ransomware.
Meanwhile, new regulations must also be assessed, along with sovereignty issues and growing third party risks.
While these challenges are ongoing, many organisations are now turning their attention to the next phase of cyber security: the zero trust model.
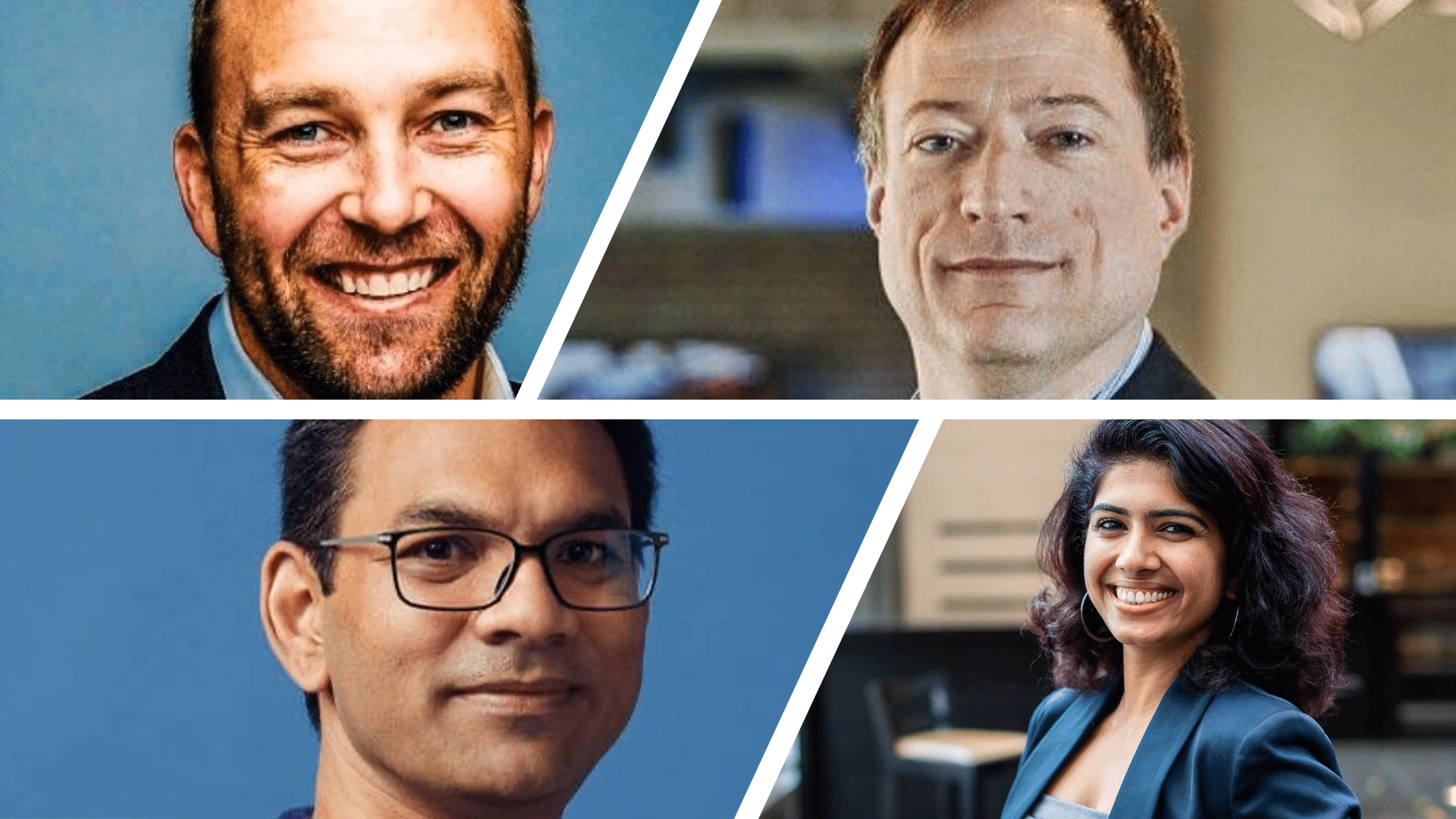
Rather than relying on corporate intrusion prevention systems, Dell Technologies’ Chief Technology Officer, John Roese, adopts zero trust security to remote working regardless of the need to harden applications against public and consumer networks threats.

From a security perspective, what I will tell you is in the remote world, the best approach to security today really boils down to a zero-trust model where you, quite frankly, shift the paradigm from trusting anybody and assume that all of your technology is compromisable.
Zero-trust is just a technology approach, but it’s not widely used, and in many cases, people are getting to it. But if you want to build that remote user, you’re out in the real world. It’s an exposed environment, and zero-trust is likely the right path.
ADAPT Research, and Advisory clients can watch Dell Technologies’ CTO full presentation on how zero trust supplements physical trust in a virtual environment.
ADAPT’s Senior Research Strategist, Aparna Sundararajan, says zero-trust frameworks must be embedded through automated due diligence processes to safeguard business assets effectively.

What do we know about trust? That trust is a vulnerability. The first thing that the zero trust framework tells us is not to trust people irrespective of who they are.
But most of the interviewees said that we work in good faith, and we trust what they have put in their questionnaires: the certifications and every other step of the process.
We absolutely, of course, are understaffed or do not have the time or even not given the time by the business to do all those checks and balances. And that, of course, adds burn to your cyber security talent.
Aparna explores how Australian CISOs focus on third-party risks in her presentation at Security Edge.
As CTO of 1.5 billion online payments business, PayPal, Sri Shivananda optimises tech-fuelled growth with the shift to a zero trust security model to protect customer and employee data.

People being in 39,000 offices worldwide, as I call them, means a completely new paradigm in terms of the safety and security of customer data, employees themselves and so on.
The endpoint attack vector now moved to homes. You have to consider a new paradigm in how you secure that.
We accelerated the journey on zero trust architecture in what we were already doing, but we accelerated that very, very quickly and put that in place.
Sri Shivananda discusses the more leading large-scale transformation of Paypal’s infrastructure into zero trust architectures.
Though a zero trust architecture is the postcard destination, Restaurant Brands International’s former CISO, Shawn Bowen, a more realistic overview of putting safeguards in place where legacy systems exist instead.

We still have some legacy pieces, but it’s about segmenting and sandboxing some of those pieces. We had a Windows XP machine that was the crane for our distribution centre. We lost our largest distribution centre in Canada for all of our coffee and pastries if that went down.
I had to live with that Windows XP, so it was about understanding that environment. Again, this is that risk perspective of what can I layer around it and use as itself and accept that it itself won’t be in a zero-trust state, but that environment has the appropriate barriers.
I don’t think we’re going to get to a ZTA, zero trust architecture, 100% for a while because many of our corporations depend on some legacy stuff. That’s about appropriately putting the safeguards in place for those.
Discover Shane’s full presentation demonstrating how security enables business resilience and customer trust.